Information leaking and stealing of your essential data cause a lot of problems for the company. Therefore, you have to be extra careful while sharing important information related to the company. And to do so, you have to ensure that you are using a secure method to keep the files safe. Whether you are sharing the files or just keeping the files on the computer, they must be safe.
You can get information about the secure ways of file sharing from FileWhopper.
Secure file sharing

Things have changed in recent years. The Internet has revolutionized several things and information transfer is one of them. While internet use has made it easy to share the files, any platform is not safe.
Your account might get hacked by the opponents or anyone can get access to the shared information. So what does this secure sharing mean? It is the online sharing of a file without the risk of online threats.
Security features
These are some of the features that you will face while using secure methods.
- Access is permission-based
- Access is password-based
- File encryption
- Two-factor authentication
- Activity monitoring of suspicious login
- Expiring links of file sharing
- Virus scanning
- Ransomware detection
Tips and solutions for business data safety
Do not ignore data protection
Data protection is vital for the wellbeing of the company. Whether your business is small scale or is expanded, some of the data is extremely important. You cannot risk the leaking of some information.
Therefore, it is crucial to take measures to make the data safe in the company. Prioritize some methods among your company employees to make sure that data sharing is safe.
Go with the business-grade system
You can find two different types of systems. The first ones are the consumer graded ones and the business graded. Consumer-grade systems are more prone to information leakage.
Therefore, businesses should definitely ignore them. It would help if you instead went for the business graded ones. They provide appropriate security controls and necessary visibility, expiring links and access controls over the data sharing.
Use cloud

Cloud services provide you with quick file sharing and implementation. There are specialized cloud services designed for businesses. You should use these services for getting ongoing agility and also the ideal setup with speed.
Training of the users

You should pay more attention to the education and training of your employees. They do not know which platform to use and whether the used platform is safe or not. They need to know these things so that they get to know the associated risks.
Besides, employees should also be aware of the highly critical data. You must let your employees know about the information that should never be shared outside of the company. Furthermore, the use of secure services must also be ensured.
Ease of use
If you are going to invest in a secure business platform or system, you should also ensure its use. If the service is a bit complicated and needs some training, train your employees. Otherwise, they won’t use it. Besides, you should also make sure that secure service is easy to be used.
Separate point solution and integrated system
You can find different services in the information-sharing systems. If the procedure only provides you with file sharing service, it is good enough. But what is you can have more in the same service? Therefore, you should go with the integrated system. Such systems provide you with email security and other services other than just file sharing.
What types of files should be shared securely?

Although every available information related to the company should be secured. But there are certain things and sensitive information that need extra care.
The list of sensitive information files include:
- Financial data
- Secret projects
- Personal information or HR
- Legal information
- Knowledge of private workers
- Acquisition and merger plans
Different secure platform services
There are specific platforms that most of the employees must be aware of. You can try out any of these methods for the usual information sharing among the company’s employees.
So here is a list of the top 5 secure platforms.
- Dropbox
- Barcode media
- Google drive
- NFC
- Shareit
Securing the cloud storage files
Cloud storage is a safe and secure method of information sharing. But if the data is too sensitive, you can try these methods.
Activate two-factor authentication
It prevents the hacker’s attacks. If you activate the two-factor authentication, your account will get an extra shield against external attacks.
What happens here is when you try to login to your account, a password or code will be sent. You will get the code on either your mobile phone or email, which you have provided. You will have to put that code in and then your account will be activated.
Make a strong password

It would be best if you went to a strong password. It is the first defense line against any external factor, whether it is hacking or something else. There are specific tips that you can follow to make your password strong enough;
- Password should be at least having eight characters or more
- Do not use any proper word
- Please do not use a name, whether it is your name or username of the account
- Always use different passwords for different accounts
- Use characters, numbers, and a mixture of upper and lower case words
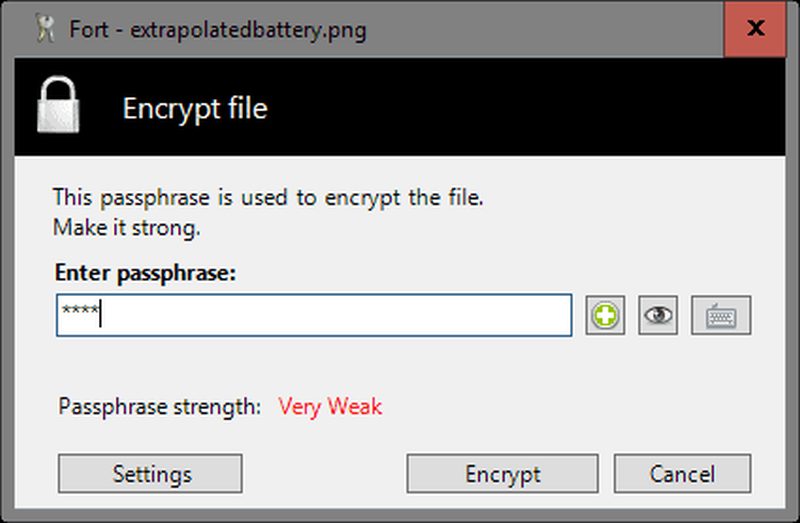
File encryption enabling
If you are using the same platform on mobile devices, make sure to enable file encryption. So if someone else got your phone, they do not get access to your sensitive information. The encryption will protect all the information present in your phone in case of theft or hacking.
To sum up
You can try out different methods of information sharing to protect your sensitive company information against hacking. Or you can try out other tips and tricks to get a secure service.


